IEC TS 62351-7 pdf download
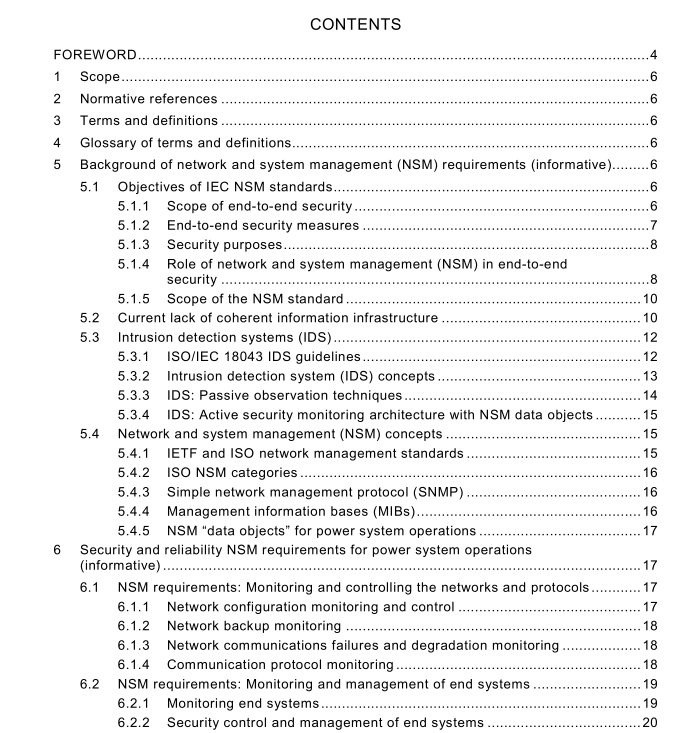
IEC TS 62351-7 pdf download Power systems management and associated information exchange – Data and communications security – Part 7: Network and system management (NSM) data object models
1 Scope
Power systems operations are increasingly reliant on information infrastructures, including communication networks, intelligent electronic devices (IEDs), and self-defining communication protocols. Therefore, management of the information infrastructure has become crucial to providing the necessary high levels of security and reliability in power system operations. Using the concepts developed in the IETF simple network management protocol (SNMP) standards for network management, IEC/TS 62351 -7 defines network and system management (NSM) data object models that are specific to power system operations. These NSM data objects will be used to monitor the health of networks and systems, to detect possible security intrusions, and to manage the performance and reliability of the information infrastructure.
The NSM data objects use the naming conventions developed for IEC 61 850, expanded to address NSM issues. These data objects, and the data types of which they are comprised, are defined as abstract models of data objects. The actual bits-and-bytes formats of the data objects will depend upon the mapping of these abstract NSM data objects to specific protocols, such as IEC 61 850, IEC 60870-5, IEC 60870-6, IEC 61 968/IEC 61 970 (CIM), web services, SNMP or any other appropriate protocol. Those mappings will need to be standardized in separate documents.
2 Normative references
The following referenced documents are indispensable for the application of this document. For dated references, only the edition cited applies. For undated references, the latest edition of the referenced document (including any amendments) applies.
IEC/TS 62351 -2, Power systems management and associated information exchange – Data and communications security – Part 2: Glossary of terms
3 Terms and definitions
For the purposes of the present document, the terms and definitions given in IEC/TS 62351 -2 apply.
4 Glossary of terms and definitions
See IEC/TS 62351 -2.
5 Background of network and system management (NSM) requirements
(informative)
5.1 Objectives of IEC NSM standards
5.1.1 Scope of end-to-end security
End-to-end security encompasses not only deliberate attacks but also inadvertent actions.
This statement is crucial to understanding the scope of this standard. Although some definitions of “security” just include the protection of systems against the deliberate attacks of terrorists or cyber hackers, often more damage is done by carelessness, equipment failures and natural disasters than by those deliberate attacks. Therefore, in this standard, “security” covers all hazards, including deliberate attacks, inadvertent mistakes, equipment failures, software problems and natural disasters. For the security and reliability of power system operations, it does not matter whether a problem was caused by a deliberate attack or by an inadvertent action.